When discussing scams and malicious activities that have utilized the linkedin.com website, I alluded to the use of fake of fraudulent LinkedIn profiles. Though it’s hard to confirm the true nature of suspicious-looking profiles, I came across several that were implicated in conducting illegitimate activities; also, several studies have used fake LinkedIn profiles to conduct security-related research.
Initiating Contact Through LinkedIn in a Targeted Attack
Two years ago the LinkedIn profile that claimed to belong to Murray Rubens was being used to establish contact with employees at a well-known technology company. The person investigating the incident pointed out that the alleged scammer’s profile indicated that he worked at the targeted company since 1997; however, the company had no record of this employee. Here’s an example of a message sent by “Murray Rubens”:
I’d like to add you to my professional network on LinkedIn. I just got involved with Linked in and I wanted connect. I really love my job at Redactedand I want to connect to as many of my collegues as possible. I want to get off to a great start. Please connect if you do not wish to connect its OK. - Murray
Such an approach can be used to target the company’s employees with social engineering, malware or other attacks.
Note the apparent inconsistency between “Murray Rubens” claiming to be at the company since 1997, yet expressing the desire to “get off to a great start.” (Thanks to the investigator for allowing me to publish these details.)
Potential Scams That Involved LinkedIn Profiles
The Ripoff Report website documents numerous reports of confirmed and suspected scams. Some of them refer to them reference LinkedIn profiles that alleged scammers used when interacting with the complaining party.
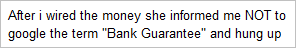
One complaint describes a scam allegedly conducted by “Ana Velasco." According to the report, "Ana Velasco" followed the transcript of a classic bank guarantee scam over the period of 3 months. The alleged scammer is reported to have baited the victim out of $25,000 “by falsifying federal investment documents, wealthy client lists, worldwide contacts (Deutch Bank) falsifying her background in commodity trading and high yield investments.” The report includes a link to the LinkedIn profile of “Ana Velasco,” which is no longer present on the site.
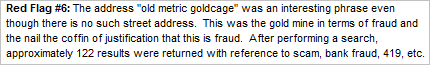
Another write-up on Ripoff Report discusses an individual, who was reportedly “posing as an investor on LinkedIn." The person who filed the complaint explained that this individual contacted him through LinkedIn regarding investing in the person’s company. The report describes a number of red flags that made the person who filed it concerned, including inconsistencies in domain registration details. However, it stops short of presenting clear evidence that the interactions initiated via LinkedIn were part of a scam.
Fake LinkedIn Profiles Set Up by Researchers
A number of studies explored people’s willingness to interact with strangers on social networking sites, potentially revealing sensitive information or otherwise exposing themselves or their employers to scams. For example, Thomas Ryan of Provide Security set up a profile of a fictitious person named Robin Sage on LinkedIn, Facebook and Twitter. The profile used the photo below and described Robin Sage as “a flirtatious 25-year-old woman working as a ‘cyber threat analyst’ at the U.S. Navy’s Network Warfare Command,” according to the Washington Times article about the experiment.

According to the paper Thomas Ryan wrote about the experiment, he used the Robin Sage profile to establish connections with “executives at government entities such as the NSA, DOD and Military Intelligence groups. Other friends came from Global 500 corporations. Throughout the experiment Robin was offered gifts, government and corporate jobs, and options to speak at a variety of security conferences.” Thomas concluded that “the propagation of a false identity via social networking websites can be rampant and viral.”
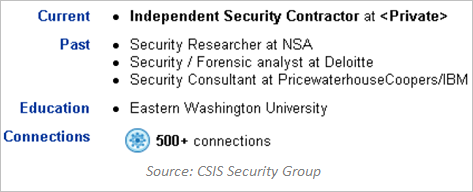
Another experiment using a fake LinkedIn profile was conducted by Dennis Rand from CSIS Security Group. Seeking to research and demonstrate the potential for information leakage through LinkedIn, Dennis created a profile of a fictitious person named John Smith, after which he sent invitations to connect on LinkedIn:
Dennis provided the text of the invitation in the presentation he created to describe the experiment:
"I found you while I was searching my network on LinkedIn and found you.
In the future I might be interested in contacting you regarding a possible job/business connections, so this is my way to keep a list of interesting people/possible future business partners/connections. …
Hope you will take the time to read my profile and accept my invite : )”
Dennis reported that “in less than 2 weeks I had build up a network of 1300+ connections with email addresses, names and a lot of information about the different large companies.”
Wrapping it Up
The nature of on-line social networking involves establishing connections with people without the opportunity to establish the person’s authenticity and reputation. Making the initial connection requires taking a leap of faith, which can easily exploited by scammers. As we saw, security researchers have demonstrated the ease with which anyone can quickly build a respectable-looking profile on LinkedIn. We also saw that miscreants can rely on LinkedIn profiles as part of a cover story when conducting a scam.
This post is part of a series that explores LinkedIn scams, fraud and information security risks. The other posts are:
- Why There Are Fewer LinkedIn Scams and Malware Than Facebook Ones
- The Potential for Malicious Ads on linkedin.com
- Exploring LinkedIn Look-Alike Email Spam Campaigns
- Scams and Malicious Activities Using the LinkedIn Website